Clop Ransomware Attacks: How Should CIOs Respond?
Ransomware targeted file-transfer software called GoAnywhere. Here are some tips for IT leaders on how to root out these types of cyber threats.
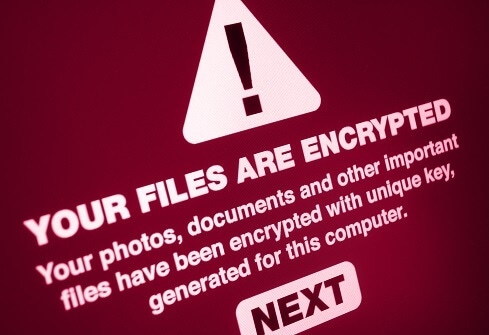
A series of cyber attacks by a ransomware group called Clop has affected a number of industries from household goods to healthcare.
The group targeted a zero-day vulnerability in Fortra’s GoAnywhere MFT file-transfer tool, which lets companies securely exchange files. Fortra released a patch on Feb. 7. More than 3,000 organizations use GoAnywhere, according to Fortra.
Procter & Gamble reported that hackers used a vulnerability in GoAnywhere MFT to steal employee information. Meanwhile, Hatch Bank reported unauthorized access to GoAnywhere from Jan. 30-31, according to The Washington Post. Other organizations affected include Community Health Systems, Hitachi Energy, data security company Rubrik, and Saks Fifth Avenue.
Clop, which first surfaced in February 2019, claims to have 130 victims, according to BleepingComputer. The National Institute of Standards and Technology identifies the GoAnywhere vulnerability as CVE-2023-0669.
Cybersecurity journalist Brian Krebs broke the news of the Clop attacks.
Ransomware is a key concern for organizations, according to the Enterprise Strategy Group research report “The Long Road Ahead to Ransomware Preparedness.” In fact, 79% of organizations reported ransomware preparedness as one of the top five business priorities for their executive team and/or board of directors, the ESG report revealed.
Here are some key takeaways on the Clop attacks and tips on how CIOs should respond to these types of ransomware threats.
Check for GoAnywhere Usage
IT leaders should check if the GoAnywhere file-transfer tool is in use, and if so, remove or upgrade it, says Ian McShane, vice president of strategy at cybersecurity company Arctic Wolf Networks.
“If they haven’t been ransomed yet, look for indicators of compromise, change all passwords and especially those that have administrative or elevated privileges,” McShane says.
Users should also apply the latest patch from Fortra.
“You really don't have an excuse for getting hit after the fix comes out, other than you just didn't apply it,” says Mac McMillan, founder of cybersecurity firm CynergisTek.
Prepare for a Resurgence
Threats from ransomware groups like Clop do not go away, McMillan warns.
“I think that's the first lesson for CIOs; what I call professional organized crime hackers just don't go away,” McMillan says. “They come back. It’s like other types of organized crime. You might cut off the head of the snake here, but it pops up somewhere else.”
So what should CIOs do? Concentrate on managing your environment and determine your level of preparedness for detecting and responding to cyber threats when they occur, McMillan says.
Know How to Speak to End Users
A key strategy for responding to ransomware attacks like the GoAnywhere incident is communicating with end users on how to report suspicious incidents when they see them. That involves a well-documented response plan, McShane says.
�“From the end-user perspective, make sure they know how to call and report it as quickly as possible, and make sure employees feel safe reporting incidents knowing they won’t be punished for mistakes or accidents,” he advises.
Will Townsend, vice president and principal analyst for research firm Moor Insights & Strategy, also advises that IT leaders have a plan ready that includes proper communication in case a zero-day or ransomware attack occurs.
“Be transparent with customers immediately and communicate the plan to address what specific information is exposed,” Townsend says. “Ambiguity can lead to disastrous consequences.”
Tighten Your Compliance Posture
Strengthening compliance with regulations should help build trust in a company’s security regimen, according to Igor Volovich, vice president of compliance strategy for cybersecurity compliance automation firm Qmulos.
“This can be achieved through continuous monitoring, regular reporting, and open communication with customers and regulators,” Volovich says. “By being proactive and transparent, companies can demonstrate their commitment to security and compliance.”
Consider Observability Tools
Companies can enable deeper inspection of their networks by using observability tools, according to Townsend. Examples include AppDynamics, Dynatrace, and Gigamon.
Follow the Zero-Trust Model
Several experts cite a zero-trust strategy as a way to guard against threats such as ransomware. The zero-trust strategy consists of “never trust, always verify.” Companies should fully authenticate and authorize users before granting access.
“Zero-trust network access applied universally is the best approach,” Townsend says. “Authenticating users to applications versus a flat network will mitigate threats.”
Perform Active Monitoring
Because the Clop attack was a zero-day occurrence, that makes active monitoring essential, according to McMillan.
“Whatever you can do to insulate yourself initially from getting hit with these things, and having good detection capabilities to react, that allows you to mitigate things if you are one of those unfortunate few that gets hit first,” McMillan says. “Your ability to respond and react and take advantage of whatever comes along after the attack to mitigate it is absolutely something you can control.”
Continuous dynamic monitoring of a company’s environment can help detect threats such as the GoAnywhere vulnerability, McMillan suggests.
“When [security teams] begin to see communication occurring that is abnormal, it alerts somebody that says, what's going on,” McMillan says. “Then if it's some sort of malicious payload, obviously, they have the ability to detect that as well.”
Limit Unessential Internet Connectivity
Limit internet connectivity for apps to only those that are most essential, McMillan suggests. An administrative interface connected to the GoAnywhere transfer tool should remain disconnected from access.
“There's a piece of this particular technology that has to be accessible to the internet to be able to transmit files -- that particular piece of this system apparently is very secure,” McMillan says. “The vulnerability was found in this administrative interface, which I think by definition, probably should never have been accessible to the internet.”
“Those organizations who implemented this technology more securely didn't have the inner administrative interface accessible to the internet,” McMillan says.
Segregate Critical Assets
Along with limiting internet access, IT leaders should also segregate critical assets on a network.
“If you've actually segregated your critical assets, you've implemented security controls like zero-trust network access, you can really limit the lateral movement if someone gets into other systems,” says Joel Burleson-Davis, senior vice president for worldwide engineering, cyber, at Imprivata.
Wipe Data from Transfer Tool
Know what your data retention and management policy entails and when using a data-transfer tool like GoAnywhere, delete data from the data-transfer tool nightly, especially critical assets, Burleson-Davis advises.
“The longer they stay on there and the longer they are unmanaged and unmaintained, the more and more likely as time goes on that those will get exposed and compromised,” Burleson-Davis says. “Be really mindful of how you're moving data around your organization and make sure that you're only retaining data on systems as long as you have to . . . and then getting rid of it.”
What to Read Next:
6 Ways Cybersecurity Can Boost Revenue
About the Author(s)
You May Also Like
How to Amplify DevOps with DevSecOps
May 22, 2024Generative AI: Use Cases and Risks in 2024
May 29, 2024Smart Service Management
June 4, 2024







